CryptoLocker Was So Successful Along Came CryptorBit
CryptoLocker was, by all appearances, amazingly successful for the cyber criminal(s) who created it. So it is not surprising that other cyber criminals wanted to join in their success.
Along came CryptorBit Ransomware, aka HowDecrypt, discovered last December. The good news about CryptorBit is that it has proven far less effective than CryptoLocker.
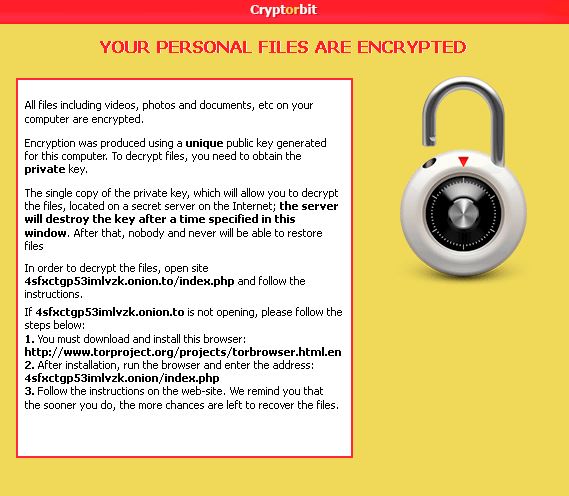
CryptorBit targets all versions of Windows. Once infected this ransomware scans your computer and encrypts every file it finds regardless of file extension. CryptorBit puts a HowDeclrypt.txt and HowDecrypt.gif in every folder that a file was encrypted in. The gif and txt files provide the victim instructions on how to pay the ransom, and like CryptoLocker payment is made in Bitcoins. The payment site appears to only be hosted on the Tor network at this point; CryptoLocker has been found to be hosted in multiple locations.
Screenshot of the HowDecrypt.gif image.
Now for the good news, CrytorBit is not encrypting the entire file, instead it’s corrupting it by replacing the first 512 bytes of the file. By appearance it’s copying the first 512 bytes of the file’s original header, encrypting those 512 bytes and storing them at the end of the file. It then creates a new 512 byte header and puts that in place of the original header. This causes a corruption in the file as the normal program that would be used to open that file can’t read this “new” header and is not able to open it. However a technique has been found that can repair the file’s header allowing the victim to recover these files. This is vastly different from CryptoLocker’s use of a 2048 bit key pair.
Another way that CrytorBit differs from CryptoLocker is that it also installs a digital coin miner, utilizing your computer to mind digital currency such as Bitcoin. As digital currency is mined using your computer’s CPU this money is deposited into the criminal’s digital wallet.
While no one is sure how the ransomware is installed reports have been that infection is happening through fake Flash updates or fake anti-virus programs. Another piece of good news is that many anti-virus programs are catching this infection, so be sure your anti-virus program is up-to-date and scanning on a regular basis.
From Bleeping Computer, “As these files are widely detected by AV programs, it has been discussed that this infection may actually be installed remotely by someone hacking into a server or computer. This would allow them to disable any AV programs, install the encrypter, encrypt your files, and then clean up the installer. This would also explain why no one has been able to find the installer for this infection.”
Should you find your computer or server infected by CrytorBit immediately contact a knowledgeable computer company. Unlike CryptoLocker the question is not is my data worth the thousands of dollars I have to pay for the private key, it’s all about finding the knowledgeable company who has the know how to repair the corrupted files!
[whohit]CryptorBit[/whohit]