CryptoWall 2.0 Now Improved
Albeit improved in all the wrong ways.
CryptoWall 2.0 is ransomware that falls into the same category as CryptoLocker, CryptorBit, TorrentLocker, the original CryptoWall, etc. As one would expect with anything labeled 2.0 there have been improvements made to the original CryptoWall, in this case making it all the more insidious.
The original CryptoWall has made plenty of trouble for network administrators, encrypting local data and any data found across network shares. There had been some loopholes network admins were using to recover the files without paying the ransom, including using data recovery to recover the original unencrypted files that CryptorWall had deleted. However, with CryptoWall 2.0 the malware developers have made changes to make things harder on their victims.
(It’s terrible, calling them developers as it almost gives them professional legitimacy. Admittedly they do consider this their job and as I’ve discussed before it is a very profitable endeavor.)
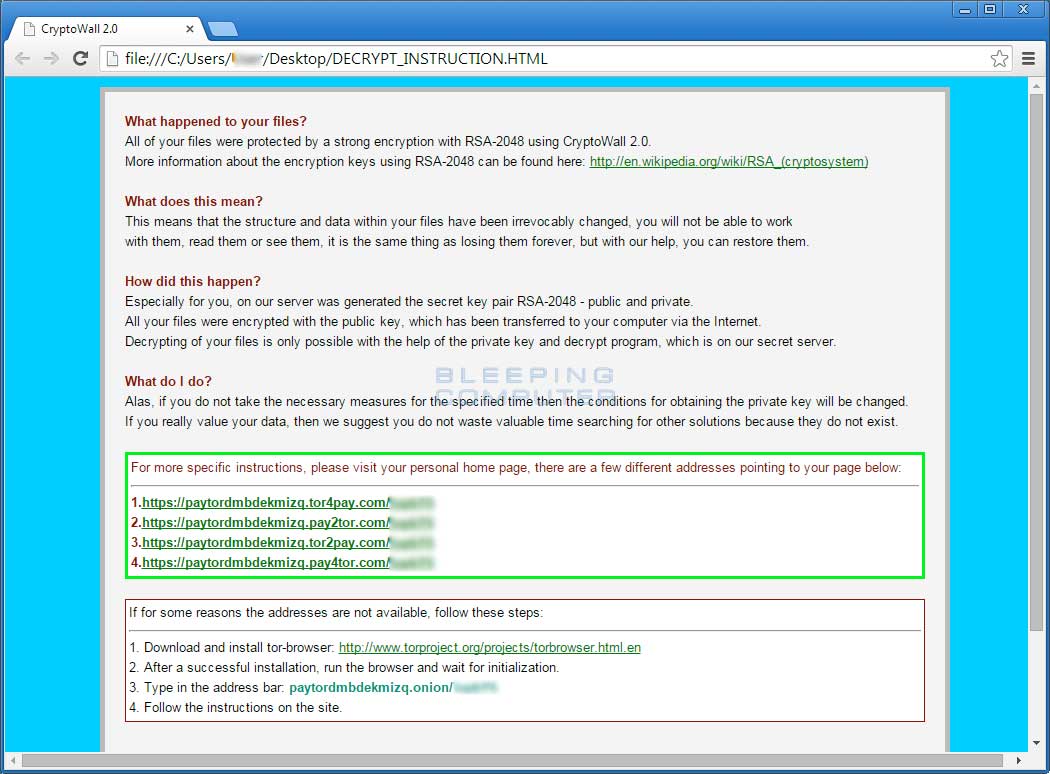
Changes included in CryptoWall 2.0 include unique wallet IDs for each victim to send ransom payments to, use of their TOR gateway, secure deletion of original [now] encrypted files, and a pretty handy FAQ / set of Instructions, which both covers what has happened to your computer and how to fix the problem. Interestingly the Instructions make it sound like these guys are hear to help and not like they are the ones who caused the problem in the first place.
Here is a Bleeping Computer image of the Instructions. Click here to read the full article on Bleeping Computer.
Always the recommended option for businesses is having a True Enterprise Backup, which allows for multiple copies your backed up material to be stored. For many this has meant that yes the backup that happened last night was just a backup of the encrypted files, but the previous version from 3 nights ago is unencrypted.
[whohit]CryptorWall2.0[/whohit]